The attack surface remains largely unprotected from Wi-Fi threats that can result in stolen credentials and sensitive information as well as backdoor/malware payload drops.
It's been nearly 20 years since IEEE 802.11b was released and the world got the first Wi-Fi-branded products. And yet the Layer 2 attack surface remains largely unprotected from dangerous Wi-Fi threats that can result in stolen credentials and sensitive information as well as backdoor/malware payload drops. Attackers have been exploiting a fundamental issue with Wi-Fi: Laptops, smartphones, and connected devices aren't equipped to distinguish between two radios broadcasting the same SSID name. This allows hackers to use malicious access points (APs) that eavesdrop on traffic, establish "man-in-the-middle" (MitM) positions, and extract sensitive information, often without leaving any traces behind.
One of the most dangerous Wi-Fi threat categories is undoubtedly "evil twin" APs, an attack technique nearly two decades old. In fact, the US Department of Justice recently charged hackers within the Russian military agency GRU with implementing evil twin AP attacks to steal credentials and "plant espionage-oriented malware" targeting organizations such as anti-doping agencies, nuclear power operations, and chemical testing laboratories.
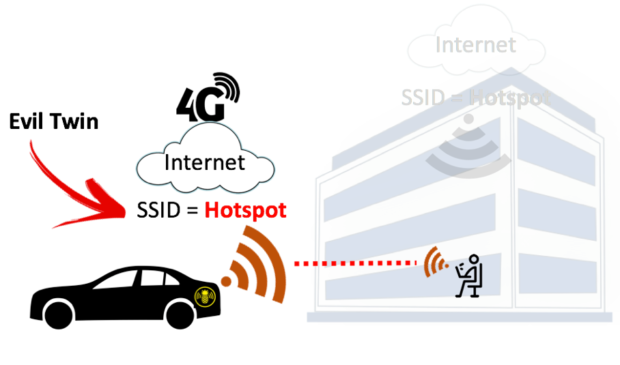
How did these GRU attacks work? The threat actor used 802.11 radios to broadcast the same SSIDs as offices and hotels in order to trick victims' devices into associating, thereby establishing their MitM position and supplying Internet service through 4G LTE connections to evade network security. Let's take a closer look at evil twin attacks to better understand defense best practices and techniques.
Analyzing Evil Twin AP Attacks
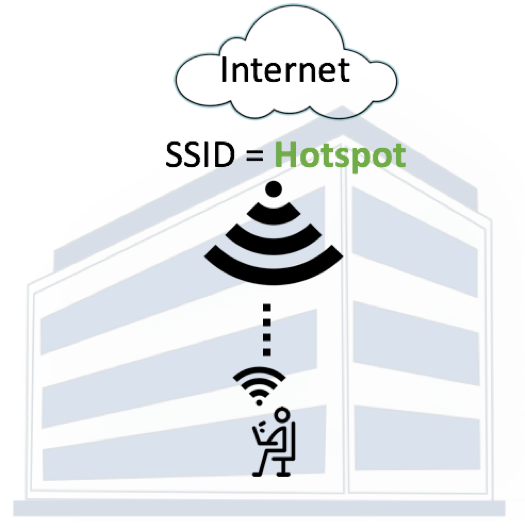
In a normal Wi-Fi connection, a person's client device (image below) associates with a legitimate AP.
When an evil twin AP is present, a threat actor broadcasts the same SSID as the legitimate AP (and often the same BSSID or MAC address of the SSID) to fool the device into connecting (image below).
In the case of the GRU evil twin attacks, hackers reportedly used a popular pen-testing tool — the Wi-Fi Pineapple from Hak5 — connected to high-gain antennas, battery packs, and a mobile 4G LTE WAN backhaul connection located in the trunks of their cars or carried within backpacks into buildings. The Wi-Fi Pineapple automates much of the labor required to set up an evil twin attack.
While within range of the target SSID, attackers begin by broadcasting the same SSID. This is straightforward and can even be done on smartphones with data plans that allow mobile Wi-Fi hotspot tethering. Attackers looking to avoid drawing suspicion toward antennas and battery packs typically opt for a popular tool called bettercap, which can run natively on Linux, Mac, Windows, and Android systems.
The bettercap command used to configure a fake SSID to be broadcasted natively from a laptop or other client is "wifi.ap.ssid."

No comments:
Post a Comment